Introduction
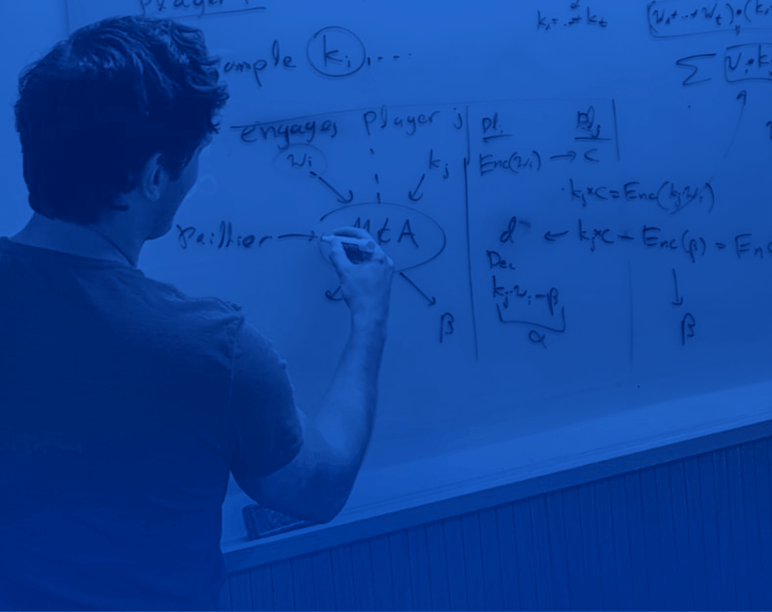
Deeper technical overview
Outline:
- Background
- Preliminaries
- Honest-but-curious protocol
- Range proofs and malicious security
- Our Protocols
- Accountability
- Security Analysis


Find out how Fireblocks helps your digital asset business to grow fast and stay secure.