If your business is looking to invest in digital assets, it’s important that you select a secure and user-friendly way to store those assets. More specifically, you’ll need to securely store your private keys – cryptographic hashes that give you access to your crypto. So, which is the best option for your organization? Hot, cold, or warm wallet?
You can use several different methods to secure your private keys – whether they’re your own, or your customers’. These methods vary in the level of security they provide, as well as ease of use and immediacy of access. In general, you’ll have to choose between using a “hot wallet” (which is connected to the internet, improving efficiency but also opening it up to certain vulnerabilities), a “cold wallet” (which is not connected to the internet, improving security while sacrificing convenience), or a “warm wallet” (which offers the efficiency of an internet-connected wallet but requires human involvement to sign transactions).
Let’s take a closer look at these different types of wallets and their relative benefits for financial institutions.
Cryptocurrency hot wallets
Hot wallets are connected to the internet, so the private keys required to sign transactions are always online. Transactions can be created and recorded on the blockchain in an automated way, without the need for human involvement.
The advantage of this approach compared to cold wallets is that users can quickly and easily trade their assets.
However, because the wallet is always connected to the internet and the keys are in a single location, this approach can be more vulnerable to theft if the security of the private key is compromised.
If you’re holding large amounts of cryptocurrency – especially customer funds – the best practice is not to keep significant portions in a hot wallet. As Gemini explains, “Although a hot mobile wallet isn’t the same as a traditional analog wallet, one similarity holds true: It’s generally a bad idea to keep a lot of money on your person. Just like you can withdraw cash from an ATM, you can send more crypto to your hot wallet when the balance gets low.”
Cryptocurrency cold wallets
Cold wallets maximize security at the expense of access speed.
The private keys are stored completely offline on a device that is not connected to the internet. Human involvement is required to digitally sign each transaction so it can be recorded on the blockchain. Stealing from a cryptocurrency cold wallet generally requires physically accessing the wallet device itself, as well as any passwords or PINs needed to open it.
Because a hardware wallet prevents your private keys from ever coming into contact with any online systems, hackers are never able to access it. The drawback is that this method is too slow to support frequent asset trading, often requiring 24-48 hours to transfer funds. It’s also difficult to scale once you have global offices that need to move funds 24/7.
Cryptocurrency warm wallets
Warm wallets combine the transaction speed of hot wallets with an additional level of security, similar to cold wallets. The keys are held online and transactions can be created automatically, but human involvement is needed to sign the transaction and send it to the blockchain.
| Hot Wallets | Warm Wallets | Cold Wallets | |
|---|---|---|---|
| Connects to internet | ✔ | ✔ | ❌ |
| Fully offline | ❌ | ❌ | ✔ |
| Requires human involvement to sign transactions | ❌ | ✔ | ✔ |
| Security | ❌ | ✔ | ✔ |
| Speed and efficiency | ✔ | ✔ | ❌ |
Not all digital asset institutions require the same balance of attributes. A crypto business that trades frequently may prioritize the speed of a hot wallet, while an investor who plans to hold assets for the long-term may value the security of a cold wallet above all.
Beyond hot vs. cold vs. warm crypto wallets
Custodians and custody technology providers are not limited to just one of these options. Some digital asset custody providers use a combination of storage methods, holding the majority of customers’ funds in highly secure offline storage, while making a smaller amount available quickly via online hot or warm wallets.
Two additional security techniques can be applied to cryptocurrency hot, cold, or warm wallets, used alone or in combination: multisignature (multisig) and multi-party computation (MPC).
Multisignature (multisig)
Requires multiple private keys to authorize a transaction, rather than a single key. The keys can be spread across several different systems, so if any single system is compromised, the owner’s assets are still protected from theft. Organizations can use multisig to create and enforce an arrangement in which multiple employees need to sign each transaction, preventing any individual from having total control over funds. This is known as an M-of-N arrangement, where N is the total number of authorized keys and M is the threshold number of keys required to authorize each payment. For example, an organization can designate five people as authorized signers and specify that at least two of them must digitally sign each payment.
While multisig strengthens security, it also has drawbacks: it’s inflexible and can be complex to manage. Once the M-of-N signature threshold for a wallet has been defined, it is fixed. To adjust the requirements as a company grows and new employees join and leave, it may be necessary to create new wallets and inform your counterparties of the new wallet address, otherwise payments could be sent to the old address and permanently lost. Furthermore, not all cryptocurrencies directly support multisig. Poor wallet implementations can introduce vulnerabilities and transaction fees can be high on blockchains like Ethereum.
Multi-party Computation
Like multisig, MPC increases security against hackers and rogue insiders by eliminating a single point of compromise. But it offers important advantages over multisig in terms of flexibility, operational efficiency, and risk management. MPC splits a private key into “key shares” that can be distributed across multiple physical devices, so a hacker cannot obtain the entire key by compromising a single device. As with multisig, this approach means a company can require multiple authorizers for transactions.
But unlike multisig, secure MPC is designed to be more flexible and scalable. For example, the authorization threshold can be changed as long as all existing key “shareholders” agree to the change. Unlike multisig, there’s no need to create a new wallet and move funds into it. Counterparties can continue to use the existing wallet address, so there’s no risk that their payments will accidentally be lost. MPC can be applied across any mix of warm, hot, and cold wallets, giving custody providers and their clients additional flexibility and security options.
Get a personalized demo
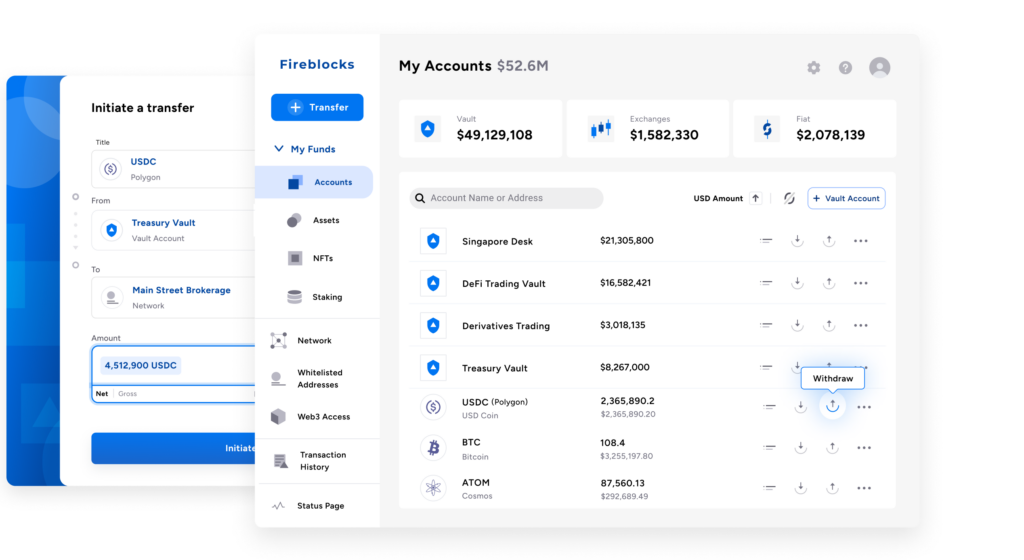
See how Fireblocks helps your digital asset business to grow fast and stay secure