On December 14, 2023, the Ledger Connect Kit was compromised, allowing attackers to drain users’ wallets on dozens of decentralized apps. Fireblocks’ customers were not impacted by the attack. Fireblocks dApp Protection, the latest security feature in our DeFi solution, detected and prevented customers from unknowingly interacting with the impacted dApps.
TL;DR
The Ledger Connect Attack began when a Ledger developer fell victim to a phishing attack that allowed threat actors to access the employee’s NPMJS account, the central hub for JavaScript code packages. The attackers used their privileged access to inject wallet-draining code into multiple versions of the Ledger Connect Kit. This software library facilitates connection between Ledger devices and decentralized apps (dApps).
Multiple dApps were then unknowingly updated to the malicious package of the Ledger Connect Kit, allowing the attackers to compromise the entire dApp front-end. This meant that any user who interacted with the dApp interface was unknowingly interacting with the attacker’s malicious code and allowed the attacker to request users to sign malicious transactions, completely draining users’ wallets.
How Fireblocks Protected Customers
Fireblocks DeFi extends our multi-layer security to protect customers against threat actors when trading, lending, and borrowing on dApps. From policy rules that govern DeFi operations to decoding that turns contract calls into human readable text, Fireblocks DeFi solution is designed to defend against attack vectors across more than 25 blockchains.
Fireblocks recently released the Early Access for dApp Protection, a new security feature that detects and alerts customers before interacting with suspicious smart contracts, phishing websites, and compromised dApps. Fireblocks dApp Protection extends our threat intelligence and security research expertise to provide customers with continual DeFi security monitoring and threat detection.
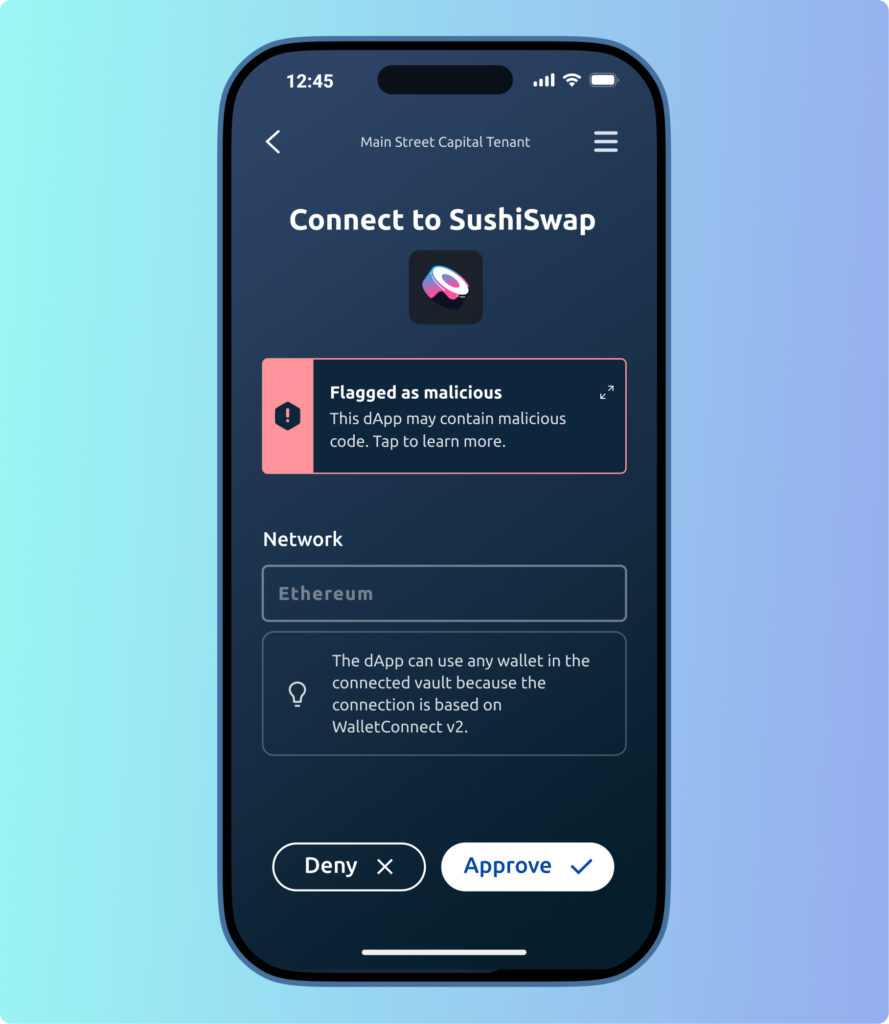
During the Ledger Connect Attack, dApp Protection identified the compromised dApp front-end and prevented customers from interacting with impacted dApps. Fireblocks dApp Protection automatically disconnected customers’ wallets from compromised WalletConnect connections to prevent further interactions.
Fireblocks’ customers can join the Early Access for dApp Protection by visiting the link here or contact their customer success manager to learn more.
Timeline of the Attack
December 14, 2023, between 10:30 am UTC to 2:35 pm UTC
- Three versions of Ledger Connect Kit were found to include malicious code, as the attacker had compromised versions 1.1.5, 1.1.6, and 1.1.7 of the package.
- The malicious code was live for approximately 5 hours.
- At 2:35 pm UTC, Ledger fixed the issue with the 1.1.8 upgrade on NPM.
Risks and the Web3 Community Response
Since dApps use the Ledger Connect Kit to support connections from Ledger devices as part of their application, all dApps users, not just Ledger users, were at risk. The presence of the package was enough for all the dApps to be compromised. Some dApp developers reacted quickly and simply took their front-end web app offline to mitigate the threat until Ledger released a patch.
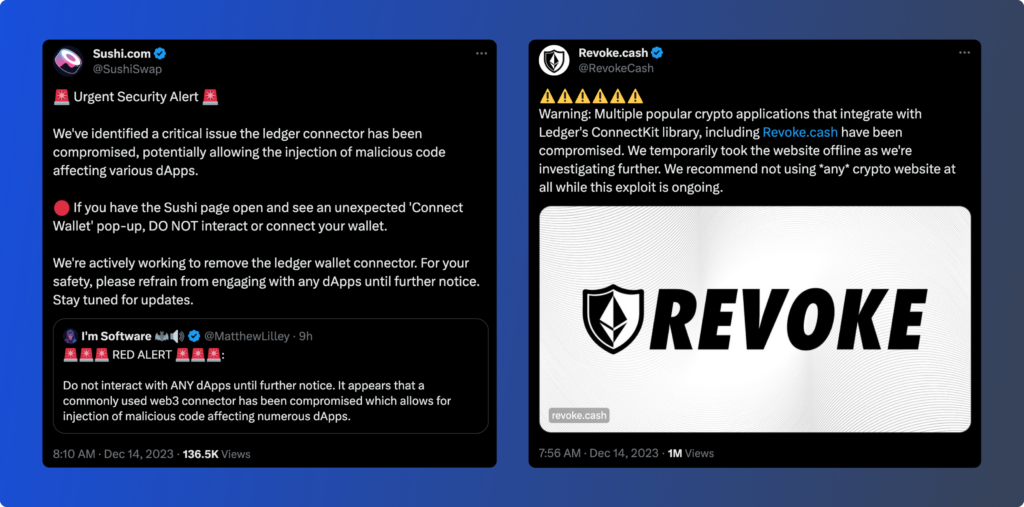
For example, SushiSwap and Revoke.cash both warned the community of the malicious code impacting their dApps and asked customers to refrain from using all dApps, or any crypto website, until further notice. SushiSwap and Revoke.cash both resumed operations once they implemented the patched library.
Fireblocks Commitment to the DeFi Ecosystem
With security at our core, Fireblocks is constantly advancing our security posture to protect customers from emerging attack vectors. It is our responsibility to customers and the industry to continually assess widely adopted digital asset security technologies, to stay ahead of potential threats, and advance the security standards of the ecosystem as a whole.
The Ledger Connect Attack highlights the complexities of building and operating secure DeFi applications. To help advance the adoption of security best practices in the DeFi ecosystem, Fireblocks recently co-authored the Rekt Test with leaders in the industry, such as Trail Of Bits and Ribbit Capital.



